About Me
My name is Mike, also known by my handle “Rem” in most internet circles. I am a SANS Technology Institute graduate, with a focus on digital forensics and incident response. I am also involved in the Python Software Foundation as a supporting member, and dedicate a large portion of time towards open source security.
Professionally, I work at Huntress as a senior security analyst by day and run a cybersecurity organization of my own called Vipyr Security by night.
I can also be found on the Python Discord, where I contribute frequently towards cybersecurity-related discussions and internal projects.
Experience
-
Huntress
PresentSecurity operations and tactical response leadership across enterprise detection and incident response workflows.
-
Senior Tactical Response Analyst
Jan 2026 - Present
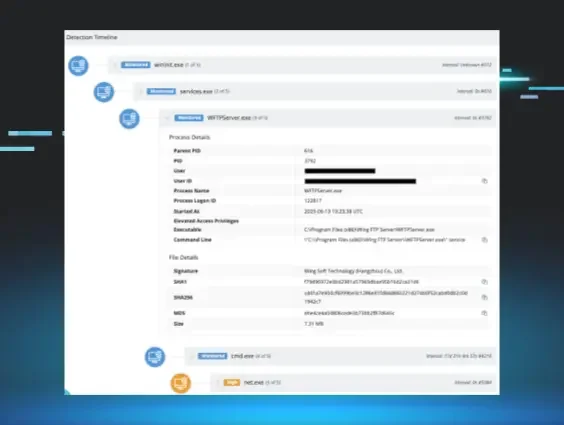
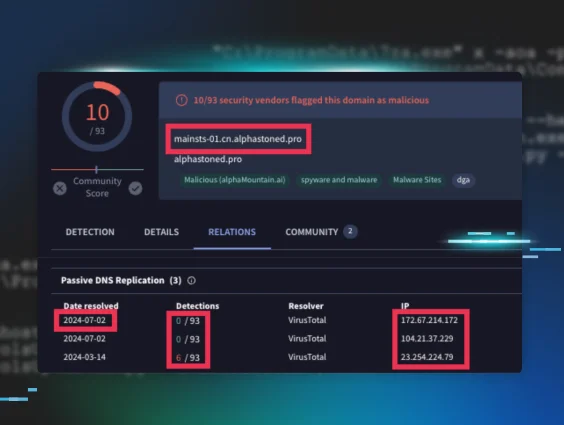
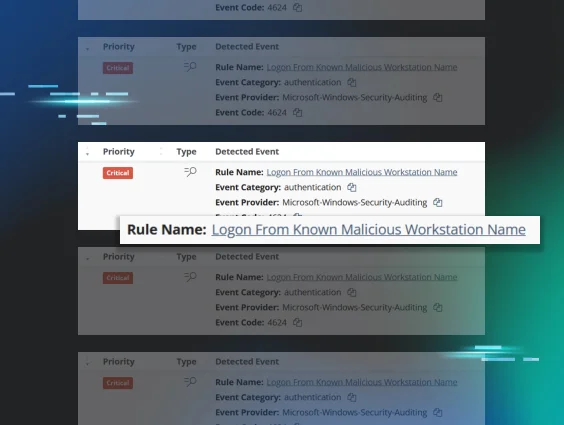
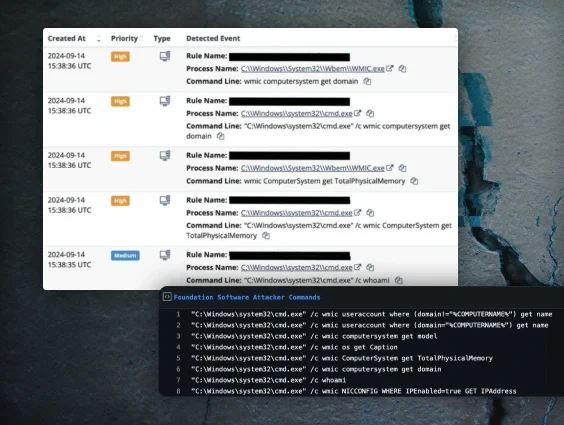
- Lead detection, triage, and active mitigation of enterprise-scale cyber threats.
- Built an AI-augmented IR pipeline with EVTXECmd and FastAPI to ingest and analyze enterprise-scale event log collections.
- Formalized iterative AI/ML workflows for KQL detection engineering and rule maintenance across incident response playbooks.
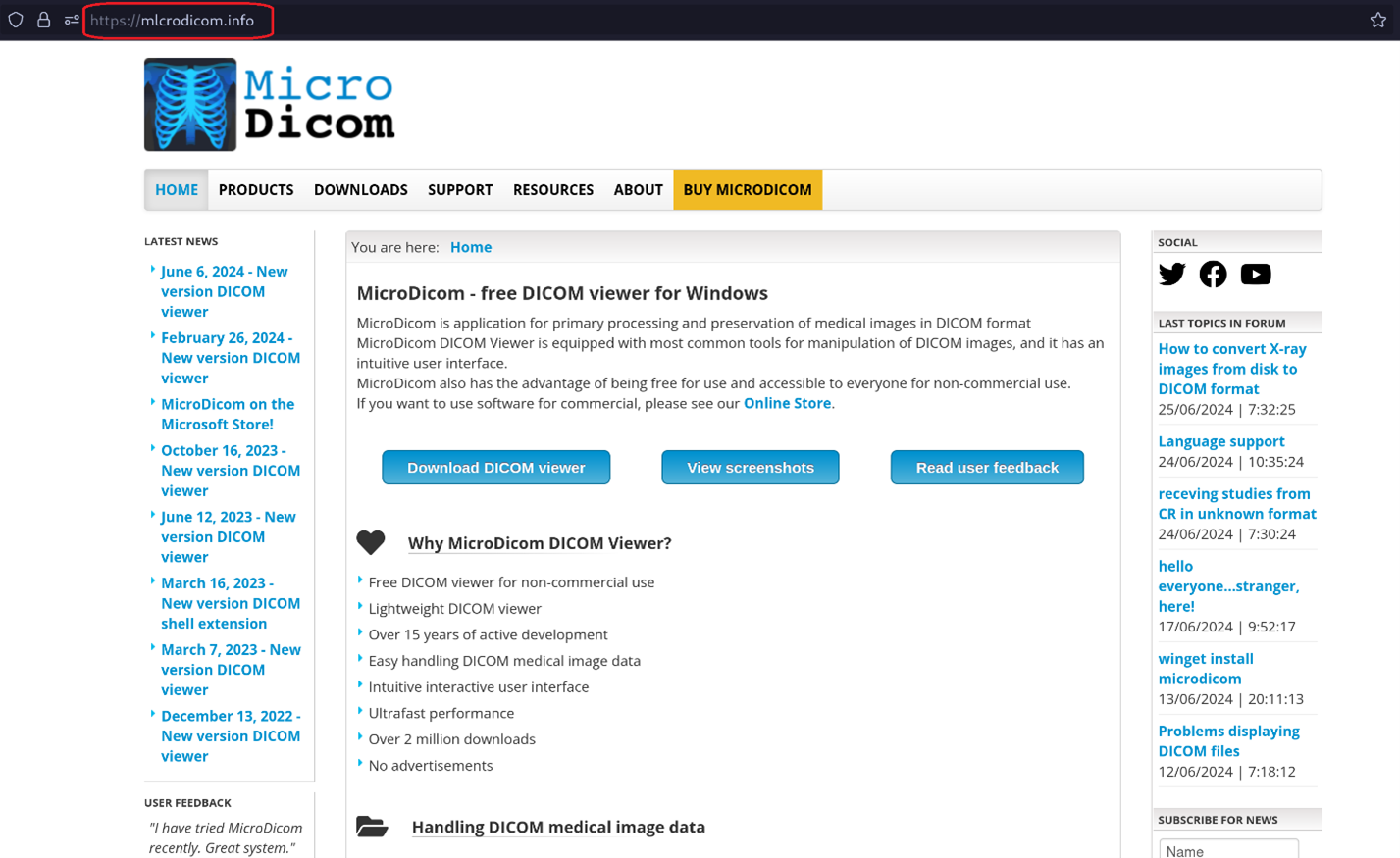
- Produce actionable threat research and advisories on emerging vulnerabilities and malware campaigns.
- Build and refine detection logic using ELK, Sigma, and YARA across detection platforms.
-
Senior Hunt & Response Analyst
May 2025 - Jan 2026
- Conducted threat hunting and incident investigation across multiple environments.
- Translated real-world incidents into documented threats and advisories for technical audiences.
- Collaborated with engineering and SOC teams to operationalize threat findings.
-
Senior Security Operations Analyst
Oct 2024 - May 2025
- Monitored security telemetry and escalated verified threats to response teams.
- Supported SOC playbook improvements informed by detection efficacy and adversary behavior.
-
Security Operations Analyst
Apr 2024 - Oct 2024
- Maintained vigilance across security alerting systems and assisted with incident escalations.
- Assisted in tuning detection systems and documenting investigative procedures.
-
-
Vipyr Security
PresentFounder and detection engineer leading practical supply-chain security operations.
-
Founder, Detection Engineer
Mar 2023 - Present
- Implement hand-written YARA schemas for at-scale Python Package Index malware detection.
- Design and evolve program specifications for a cluster-based code security engine.
- Drive incident triage and mitigation workflows for open-source package threats.
-
-
Wells Fargo
Risk analyst supporting financial controls through data validation and reporting.
-
Risk Management Analyst
Apr 2023 - Jun 2023
- Performed data reconciliation and deviation analysis using SQL and Python.
- Authored secure, maintainable tools for internal data pipelines.
- Supported PowerBI and Excel workflows with Python, PowerShell, M, and SQL.
-
-
United States Air Force
Program analyst supporting secure systems operations and compliance.
-
Program Analyst
2015 - 2023
- Performed software testing, IT asset management, and configuration management.
- Supported software distribution lifecycle operations and physical penetration testing.
- Managed secure systems and oversaw unit-level IT compliance auditing.
-
Certifications and Education
- GIAC Enterprise Penetration Tester (GPEN)
- GIAC Certified Forensic Analyst (GCFA)
- GIAC Certified Forensic Examiner (GCFE)
- GIAC Certified Intrusion Analyst (GCIA)
- GIAC Python Coder (GPYC)
- GIAC Certified Incident Handler (GCIH)
- GIAC Security Essentials (GSEC)
- GIAC Information Security Fundamentals (GISF)
- GIAC Foundational Cybersecurity Technologies (GFACT)
Publications and Referenced Work
See the blog section for full write-ups and referenced technical work.
Accolades
- Deans List - SANS Institute Fall 2024
- Deans List - SANS Institute Spring 2024
- PicoCTF 2024 - 138/6957, Global Leaderboard
- NCL Spring 2024 - 33/7412, Individual
- NCL Spring 2024 - 7/4199, Team (Team Captain)
- GIAC Advisory Board
Getting in Touch
The simplest way to contact me is through @sudo_Rem.